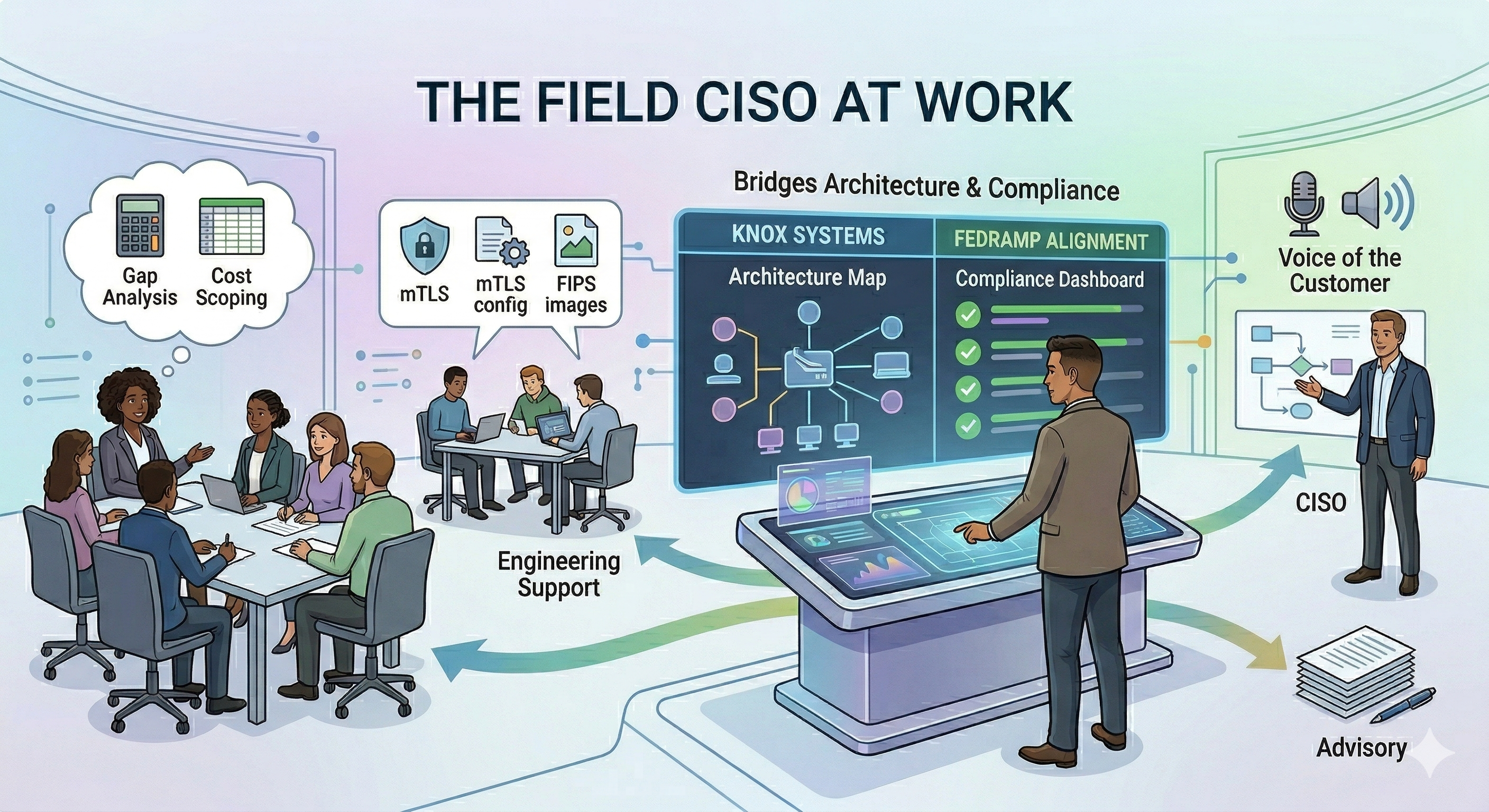
What the Field CISO Role Looks Like in Practice
Phil Venables published a piece this week titled “The Real Role of the Field CISO.” It’s the most thorough description of this role I’ve come across, and reading it felt uncomfortably like someone had been watching my calendar.
I’ve been the Field CISO at Knox Systems for a month now, and I want to use his framework as a lens to describe what this role actually looks like from inside it, specifically at a company whose product is a FedRAMP shared boundary and whose customers are Cloud Service Offerings (CSO) trying to reach the federal market.
A quick word on Knox’s model, because it shapes everything that follows: Knox manages the largest federal cloud, sitting across the three main hyper scalers. We support: FedRAMP Moderate, FedRAMP High, and DoD IL4/5 ATOs. CSOs don’t build their own FedRAMP package, they deploy into Knox’s boundary, inherit a significant portion of the control set, and get listed under our authorization, allowing them to reach federal agency customers in a fraction of the time and cost of going at it alone. My job is to help prospects understand it, help customers succeed inside it, and feed what I learn back into the organization.
With that context, here’s how Venables’ framework maps to my day to day.
Sales Support
This is where most of my customer-facing time goes right now. When a prospect’s CISO asks “what does FedRAMP actually cost us to maintain?” or “which of our controls are inherited versus customer-owned?”, those are questions that need a technical practitioner in the room. That’s where I come in.
I do architecture gap analysis calls with prospects, walk through their current environment, identify where their stack fits against the Knox boundary, and produce a written gap analysis they can take to their leadership. The goal is helping them make an informed decision and doing that honestly, even when the answer is “you have more work ahead than you thought,” builds more durable trust than a polished pitch ever could.
Venables describes Field CISOs as the people who can articulate the “intrinsic risk mitigations that come built in.” In the FedRAMP context, that means being able to explain control inheritance, what “customer-managed controls” actually requires of their team, and what the path to an ATO looks like from where they’re standing today.
Post-Sales Support and Onboarding
Once a customer decides to deploy on Knox, the questions don’t stop, they get more specific. Container registry placement, CI/CD pipeline boundary decisions, FIPS-validated image requirements, mTLS configuration for service-to-service communication. These aren’t abstract compliance questions; they’re architecture decisions with real implications for their authorization.
Having someone they can call with those questions, and who can actually answer them, is one of the highest-leverage things I can offer. Getting those architecture decisions right early keeps the deployment and authorization processes moving forward.
Voice of the Customer
Venables identifies this as one of the most powerful and distinctive activities of a Field CISO: representing what customers actually need back to the organization, not just validating existing roadmaps.
I’m still early in my journey at Knox, but I’m already accumulating signal. When I see the same sub-processor questions come up across multiple prospect calls, that’s a cue to sharpen how we walk customers through that evaluation together. When there’s confusion about where the Knox boundary ends and the customer’s responsibility starts, that’s a prompt to refine how we guide them through scoping. When FIPS validated module questions surface repeatedly, that’s a signal to get ahead of it earlier in the onboarding conversation. The patterns I see across engagements inform how we collaborate with the next customer.
My job is to make sure those signals don’t stop at me. They go to the architects, the product team, the executive team. The Field CISO is only as useful as the feedback loop they maintain internally.
Research, Training, and Education
This is where my writing fits in. I publish at OneUpSec.tech, posts on FedRAMP modernization, supply chain security, GRC engineering. I’m active on LinkedIn, not to market Knox directly, but to contribute genuine perspective on topics I spend my days inside.
Venables frames this as boosting brand and trustworthiness by delivering useful content. I’d frame it slightly differently: it’s how I stay sharp, stay visible in the community I serve, and demonstrate that what I know is current. A Field CISO who stops learning stops being credible. Writing forces me to think rigorously about the things I’m advising customers on.
There’s also something to be said for accountability. When I publish a take on FedRAMP modernization or supply chain security, I’m putting a stake in the ground. That keeps me honest and keeps me up to date on the ever-changing field.
Consulting and Strategic Advisory
A significant portion of what I do is consulting. Gap analysis writeups, follow-up documentation after architecture calls, CUI boundary scoping guidance when a customer CISO raises a question their team can’t resolve internally. Venables notes this often needs to be short-lived as companies build out professional services capacity but for now, and for the right customers, it’s some of the highest-value work I do.
Audit and Regulatory Support
In a FedRAMP context this isn’t a supplemental activity, it’s structural. The whole customer relationship is oriented around an authorization process. Helping customers understand what evidence they need to produce, what controls they own versus inherit, how ConMon works inside the Knox boundary, that’s not a back-office function. It happens in the same conversations as everything else.
On the Individual Characteristics Venables Describes
He lists a handful of traits that define great Field CISOs as individuals. A few land for me personally.
Lived experience and empathy: I didn’t come to this role from consulting. I came from operating as an Air Force Cyber Systems Operator, then through practitioner roles and most recently at Aquia where I led a cATO program for a large federal civilian agency. I’ve been on the other side of the table. I know what it feels like to be a CISO staring at a FedRAMP requirement document trying to figure out what it actually means for your team’s workload. That empathy isn’t manufactured.
Boardroom bilingual: I’ve had days at Knox where I’m in a technical architecture discussion about Kubernetes network policy in the morning, a CISO briefing on control inheritance in the afternoon, and writing a post-call summary for an executive in the evening. The range is real. You have to be comfortable in all of those registers.
Humble but value-proving: This one I think about a lot. The Field CISO who walks into a customer conversation trying to demonstrate how much they know is going to lose the room. The one who walks in genuinely trying to understand the customer’s problem and then delivers something useful and tailored to the customer, is the one who gets invited back.
The Bottom Line
Venables’ framework is right. Field CISOs exist to build and maintain customer trust through competence, empathy, and a genuine commitment to customer outcomes not just customer acquisition. Every activity he describes, I can find in my own work at Knox.
The thing I’d add, from inside this specific role: when your product is federal compliance infrastructure, the trust you’re building has formal structure around it. The authorization process, the control inheritance, the ConMon obligations, these aren’t background conditions. They’re the thing, and the Field CISO who can navigate that technical and regulatory complexity while staying genuinely customer-focused is the one who moves the needle.
If you’re a CSO trying to figure out your path to the federal market, Knox exists to make that journey faster, less expensive, and less painful than going at it alone. Our shared boundary model means you inherit the hard compliance work we’ve already done, and I’m here to help you understand exactly what that means for your product and your team. If any of this resonates, I’d genuinely like to talk.
Mario Lunato is the Field CISO at Knox Systems. He writes about FedRAMP, supply chain security, and GRC engineering at OneUpSec.tech.